I'm excited to share that Anders Carlsson and I will be presenting our talk, "The Attribution Story of WhisperGate: An Academic Perspective," at the VB2025 conference in Berlin, 24–26 September 2025. 🤓
In this talk, we'll explore how AI/GenAI can assist in tackling the complex challenge of cyberattack attribution, using the WhisperGate incident as a case study.
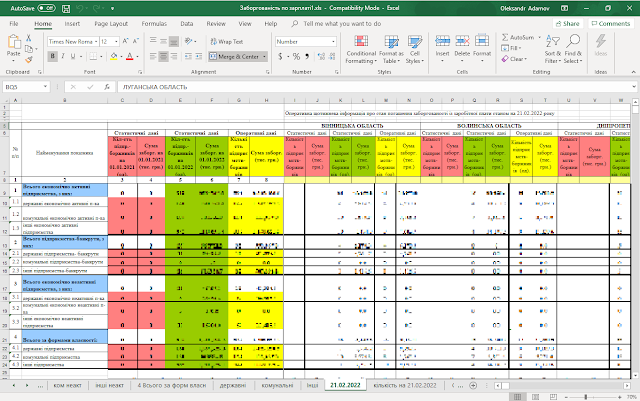
WhisperGate is a destructive malware campaign executed on 13 January 2022 against the government infrastructure of Ukraine. It was attributed to the Russian state-sponsored threat actor linked explicitly to the Ember Bear group by CrowdStrike on 30 March 2022 [1] and to Cadet Blizzard by Microsoft in April 2022 [2]. It was associated with Russia's Main Intelligence Directorate of the General Staff (GRU). These APT group(s) have never been seen before, and it was unclear which GRU unit this campaign was associated with. ESET, in its turn, attributed the majority of wiper attacks against Ukraine in 2022 to Sandworm, another GRU-associated APT group (Unit 74455) [3], "with varying degrees of confidence" [4].
Only two years later, in September 2024, Maryland's Grand Jury unsealed a superseding indictment [5] against five members of GRU's Unit 29155 (a.k.a. Ember Bear) and one previously charged, in June 2024, Russian civilian Amin Stigal [6] for a cyber operation called WhisperGate [7] against the Ukrainian Government services and its allies in the US and Europe – at least 26 NATO countries. It was the first time GRU's Unit 29155 was mentioned as a cyber actor.
According to Bellingcat [8], this unit is famous for its assassination and sabotage operations abroad rather than cyberattacks, such as the Salisbury Poisonings – a failed assassination attempt on Sergei Skripal, a former Russian military officer and double agent for British intelligence, using a nerve agent. The attack, which also poisoned his daughter Yulia, took place in Salisbury, England, on 4 March 2018. [9]
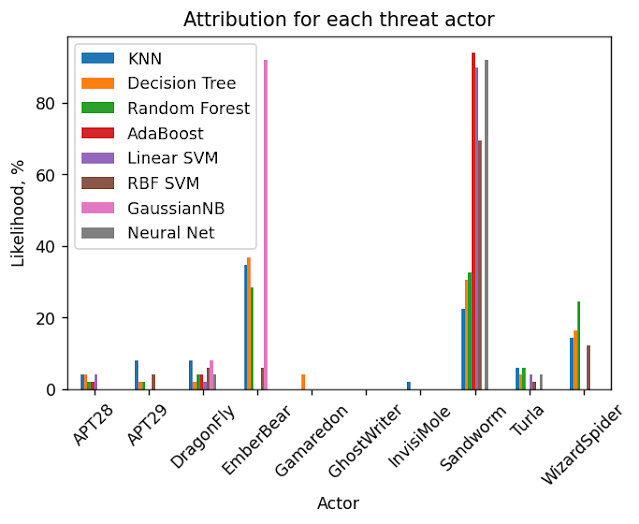
Now that WhisperGate's attribution is well-established, we can retrospectively apply and compare different attribution approaches – manual analysis, traditional supervised machine learning classification, and LLM-powered attribution – to evaluate their effectiveness and determine which categories of Indicators of Compromise (IoCs) have the most significant impact on correct attribution decisions.
References
[1] https://www.crowdstrike.com/blog/who-is-ember-bear/
[2] https://www.microsoft.com/en-us/security/blog/2023/06/14/cadet-blizzard-emerges-as-a-novel-and-distinct-russian-threat-actor/
[3] https://attack.mitre.org/groups/G0034/
[4] https://www.welivesecurity.com/2023/02/24/year-wiper-attacks-ukraine/
[5] https://www.justice.gov/opa/pr/five-russian-gru-officers-and-one-civilian-charged-conspiring-hack-ukrainian-government
[6] https://thehackernews.com/2024/06/russian-national-indicted-for-cyber.html
[7] https://www.nioguard.com/2022/01/analysis-of-whispergate.html
[8] https://www.bellingcat.com/news/uk-and-europe/2021/04/26/how-gru-sabotage-and-assassination-operations-in-czechia-and-bulgaria-sought-to-undermine-ukraine/
[9] https://en.wikipedia.org/wiki/Poisoning_of_Sergei_and_Yulia_Skripal